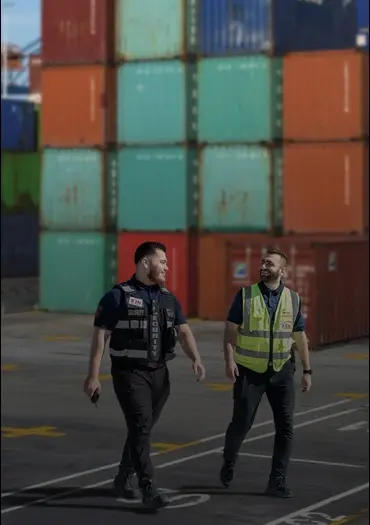
Our Team Are Always Active24/7




Our Team Are Always Active24/7
About ICORP Security
Striving for Excellence in Every Way
ICORP Security was established in January 2018 with a clear mission: to empower safety through innovative security solutions and exceptional service. Based in Victoria, we proudly serve a wide range of sectors across Australia and New Zealand, providing comprehensive, tech-supported, and cost-efficient security services.
Our commitment to excellence, innovation, and customer satisfaction has positioned us as one of Australia's most trusted security companies, centred on:
Client & Employee Safety
Ensuring the well-being of those we protect through vigilant, proactive measures.
Regulatory Compliance
Adhering to the highest standards, keeping our services in line with industry regulations.
Strong Relationships
Building lasting partnerships with clients and communities, based on trust, integrity, and mutual respect.
By integrating cutting-edge technology and a proactive mindset, we ensure that our clients receive the highest standard of security, every time.

CASE STUDIES
How We Improve and Enhance Security at Client Sites
Explore our case studies to see how we elevate security at client sites with tailored solutions, innovative technology, and expert strategies for optimal protection.
Need Support in
Your Daily Security Operations?
DISCOVER YOUR SOLUTIONWhat Our Clients Say
Real Feedback from Our Happy Clients
We believe the best measure of our success is the satisfaction of those we serve. Here’s what our clients have to say about partnering with ICORP Security.
We Work With
OUR MEMBERSHIPS & CERTIFICATIONSWe Uphold Best Practices and
We Uphold Best Practices and
Compliance

Australian Business Events Association

Australian Security Industry Association Limited

Compliance Management

International Organization for Standardization
Questions & answers
Frequently Asked Questions
- What type of training and licensing do your guards have?ICORP guards are fully licensed, trained to Australian compliance standards, and equipped with certifications such as First Aid, RSA, and Working With Children Check.
- Do you provide security for large events?We provide security for events of all sizes, offering crowd control, RSA, asset protection, VIP escorts, traffic control, and other tailored solutions.
- Can you provide security for my office/apartment buildings?Yes, we provide security for commercial and residential buildings, managing concierge desks, after-hours services, and other tailored security solutions.
- How does your pricing structure work?Our security service cost depends on hours required, location and guard responsibilities. Contact us for a no-obligation consultation and/or request a quote.
Australia's Leading
Security Service Provider

DISCOVER WHAT’S NEW ON OUR BLOG